
Overview of SCA Tools: Core features and benefits of deployment

Software Composition Analysis (SCA) is a solution that helps organizations handle the management of open source components. Like any other new kid in the block, there are questions left unanswered about SCA.
In this blog post, we will shed light on the core features of SCA tools, their direct benefits, and the various challenges SCA tool vendors face.
What is an SCA tool?
SCA tools are applications that support software development teams to ensure license compliance and improve the security of the code. At a high level, they perform automated scans on source codebases. The tools also help the team identify open source components, their license, and flag any known vulnerabilities.
Core features of SCA tools
There are two core features offered by vendors, including license compliance and security vulnerability mitigation. We will discuss both of them briefly below.
Management of open source compliance
Organizations adopting open source software in their products and services establish compliance programs to adhere to the licensing. This task can be time-consuming especially given the large-scale adoption of open source across all industries.
SCA tools provide a certain level of automation to help organizations keep pace with the development activities while remaining compliant. The features in any SCA tool from a compliance perspective include the following five core functionalities:
- Detecting open source source code within the scanned body of code
- Identifying the licenses of the discovered open source code
- Flagging potential licensing conflicts
- Recommending remediations actions for any identified issues
- Implementing and managing the compliance workflow within the organization
There are undoubtedly many other features from a compliance perspective that SCA tool providers offer. It is worth mentioning that functionalities also vary from one vendor to another, with the above five features being the underlying core.
Identify and help mitigate security vulnerabilities
In addition to the abovementioned list, SCA tools now offer another subset of functionalities dedicated to software security.
Given a large number of open source contributors and, in some cases, unknown origin, organizations emphasize the security aspects. Hence, in the past few years, several vendors started to incorporate security as part of their offering. The essential functionalities provided by SCA tools from a security perspective include the following:
- Harvesting and storing security vulnerabilities information from multiple sources into their database, often referred to as security knowledge base
- Detecting any security vulnerabilities in the scanned code that correspond to the known vulnerabilities tracked in the knowledge base
- Detecting vulnerabilities in dependencies – for instance, if software package A depends on Library B, the tools alerts the user of a possible security vulnerability in Library B
- Recommending remediation actions when possible, such as a new patch that is now available or upgrading to a recent version
- Continuous monitoring of managed repositories for any new security vulnerabilities that may be discovered in the future
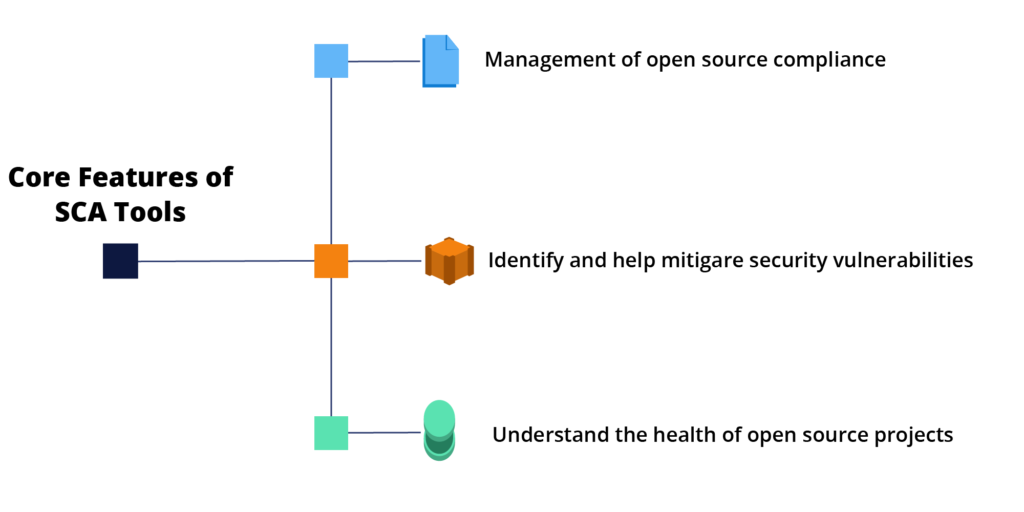
Understand the health of open source projects
There is a different variety of functionalities that uncovers critical metrics about the health of open source projects. This category is novel and pioneered by Debricked as part of their SCA tool offerings.
With the growing adoption of open source, organizations continuously discover that they depend on open source projects. The best approach to such situations is to uncover the metrics concerning the project’s health to assess if it is suitable to adopt the project or not. Project health metrics functionalities include the following three core areas:
- Understanding specific project health ranking
- Learning about possible risks concerning project activity
- Automating the curation of open source components based on their health metrics
How do SCA tools work?
Despite the varying supported and advanced features, most SCA tools follow a similar operating model. They scan the source and apply their proprietary algorithms to match it with code in their knowledge base. The tools also generate an inventory of all discovered open source packages, their origin, license, and dependencies. Lastly, an inventory of any known vulnerabilities can also be generated by such tools.
From a compliance perspective, SCA tools provide information on each package, such as the package name, version, and license. The tools also alert the users in the event of licensing conflict as defined by the organization’s policies.
To help organizations stay secure, the tools would flag security information concerning each package. This information contains such as an inventory of discovered security vulnerabilities, their severity, prioritization information, and in some cases, suggestions for remediation.
Similarly, from a project health perspective, SCA tools would uncover several metrics. These metrics cover the areas of project activities, contributors, participating organizations, the flow of commits, diversity and inclusion metrics, code evolution, and risks.
Why do companies need SCA tools?
With the increased adoption of open source, there is an expanding need for license compliance and a low-security risk profile. SCA tools help organizations with both of these goals by allowing them to:
- Adhere to open source license compliance requirements
- Identify and remediate exposure to security vulnerabilities
- Generate a Software Bill of Materials (SBoM) to be used up or down their software supply chain
- Ensure adherence with company policies concerning licensing compliance and internal secure coding guidelines
- Gain a deeper understanding of their software stack by identifying reliance on open source software
- Manage the governance aspect and workflow of approval of using open source software on products and services
Given the growing number of providers, it’s becoming increasingly challenging to compare all the available tools. It is for the most part virtually impossible to determine which one would correspond to the needs of your organization. This challenge is compounded by the fact that the offerings from a functional perspective can differ quite significantly. Our guide on how to evaluate and benchmark SCA tools can be used as a starting point.
Other benefits of using SCA tools
Beyond the direct benefits, there are many indirect benefits of a strategic value. Such indirect benefits include:
- Enabling innovation by facilitating open source adoption
- Helping maintain a secure codebase
- Managing risks incoming via third-party software providers
- Enforcing organization’s open source policies and processes
- Moving open source use from ad-hoc to a standardized process
- Helping organizations build trust relations in their software supply chain
Typically organizations adopt SCA tools for their immediate and direct benefits. They also enjoy the many positive side effects shortly after integrating the tool with their development efforts.
Key challenges of SCA tools
Like any other software tooling, there are challenges in the space of SCA tools. These challenges vary from one vendor to another and one adopter organization to another. In the following sections, we explore the key challenges.
Discovery accuracy
There is a need to improve the accuracy of SCA tools when identifying the origin and license of the code. In addition, they also need to keep their vulnerability databases up-to-date in order to identify all known vulnerabilities mapped to the scanned source code.
There are other challenges concerning the improved discovery of security vulnerabilities. It is not necessarily static vulnerable code that is not being run, but the one that is being called and executed during runtime.
Dynamic licensing landscape
In the past few years, we’ve witnessed a new open source licensing experiment. Several technology startups are working to monetize the open source projects they’ve founded using innovative licensing models.
This situation has paved the way to a new school of thought called Open Core. Open Core advocates for an approach that is somewhat not as clear-cut as proprietary versus open source. It offers a blend of open-source and proprietary software. The core platform remains free and open-source (with minimal features/functionality). Paying enterprises can then choose to pay for add-on services or unlock proprietary, feature-rich capabilities.
This dynamic has an overall impact on the open source licensing landscape. New licenses are introduced and ambiguously billed as open source licenses, whereas existing licenses are modified to incorporate new clause(s). As a result, dozens of projects have to update their licensing terms. All of these factors have huge implications on organizations that should ensure compliance with the various applicable licenses.
Data accuracy
Data quality is an ongoing issue with knowledge bases and vulnerability information. Most SCA tools maintain databases of known open source code and declared security vulnerabilities. Keeping the data’s accuracy is an ongoing challenge and directly impacts the security of the code deployed.
Standardized Software Bill of Materials
With the recent executive order from the Biden administration, we expect to see several efforts to consolidate and drive towards a standardized set of tooling to produce the SBoM. Furthermore, we believe new functionalities will emerge in data collection, data manipulation, and customized formats. There will seemingly be improvements to the various forms used to represent the data.
Automation
Full automation of the compliance and security process is an ongoing challenge. However, we expect this challenge to be addressed with AI and Machine Learning technologies in the next few years.
With hundreds to thousands of developers in any given organization using open source, it is necessary to automate the process of compliance as much as possible. Similarly, the organization should also automate the ability to flag security vulnerabilities discovered in the codebase.
Enablement of Established Workflows and Policies
The target goal for an SCA tool is to empower developers without slowing them down or breaking their workflow. We believe there are many desired improvements in this space.
API & Integration with Build Systems
With a growing number of build systems, package managers, and programming languages, SCA tool vendors are under continuous pressure to support them all. All of these developments pose certain limitations for the vendors and are areas for improvement.
Debricked’s SCA solution
With the increased reliance on open source, it is becoming indispensable to run a software development operation without the assistance of an ongoing software composition analysis.
Debricked offers an SCA solution that helps companies and developers build a healthy application while keeping security risks at bay. We’d love to do the same for you. Create a free account and work with open source securely today!



“Want to stay up to date with our lastet news and products?” – please correct the typo.
Thanks a lot for pointing that out, it has been corrected 🙂