Here are the steps you need to follow after creating an account with Debricked:
- Set up an integration
If you have a dependency file of a project, but setting up an integration is not applicable at the moment, you have the option to upload the dependency file manually - Set up a license use case
The first time you visit the license view, you'll notice that all repositories will be set to "Unknown" in the risk column.This is because you have not yet configured any use cases for your repositories. Setting a use case lets the tool know how you distribute the code in each of your repos, which has an impact on the risk of any given license.
- Set up automations
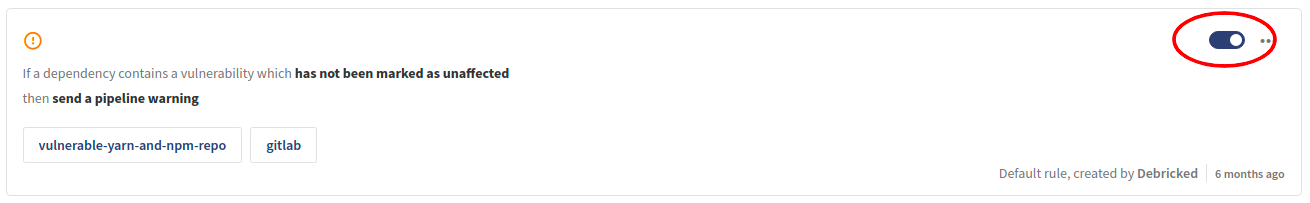
The automations engine allows for rules to be triggered based on conditions. For example, a rule can fail a pipeline if there is a new high-risk vulnerability detected, or an unwanted license.By default, Debricked has set up 4 rules for you to prevent unwanted licenses or dangerous vulnerabilities.
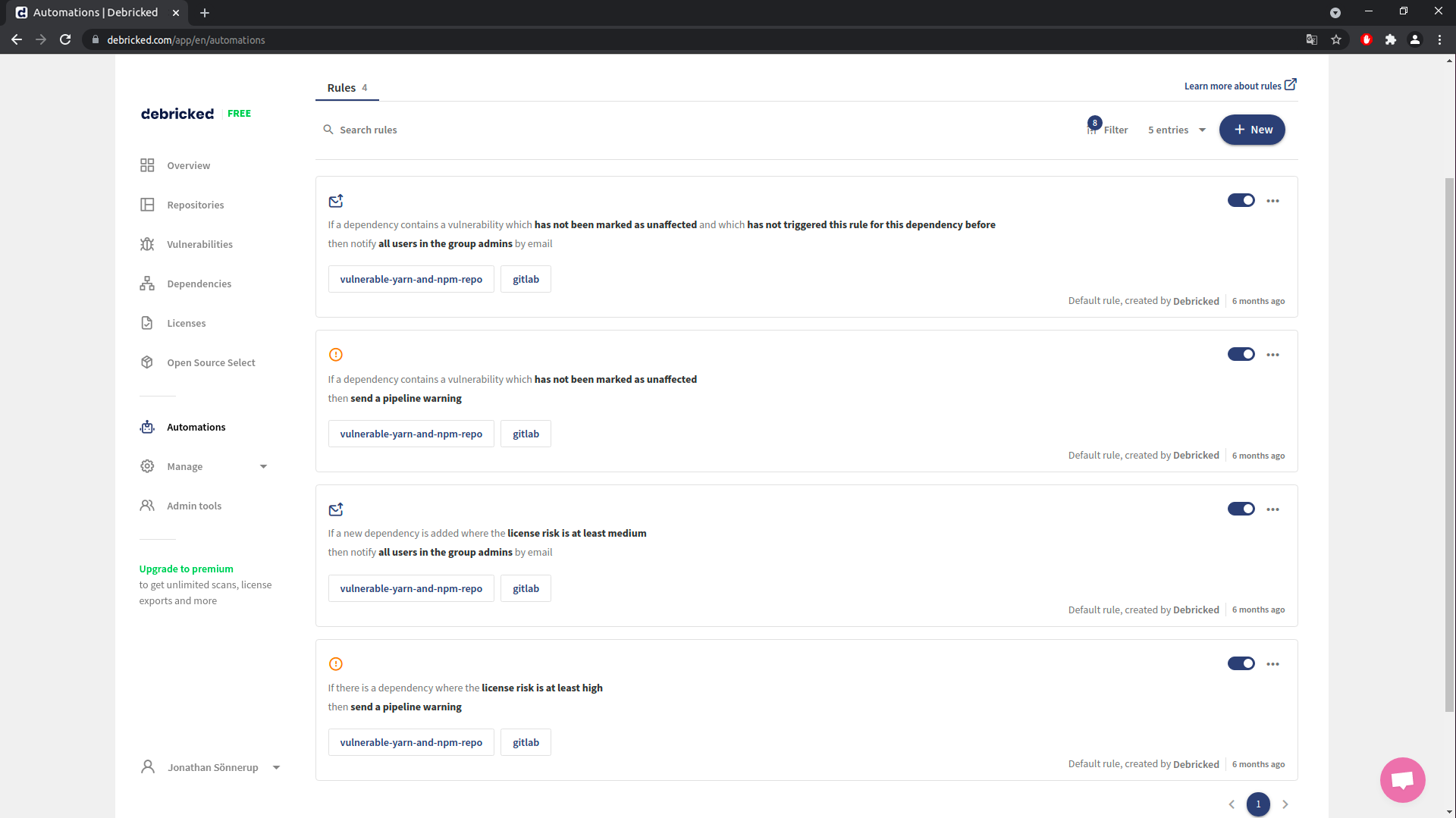
They can easily be disabled by clicking the toggle button.