
Post Summer Product Updates: 2021 Edition
Today is the first day that I had to wear gloves on my bike ride to work, marking the definitive end of summer. Seems like a fitting time to reminisce and have a look back on what got built during summer. Deceptively short as the Swedish summer might be, in the Debricked office, a lot got done!
Dependency tree visualizations
Understanding the context of how a vulnerable dependency got introduced to your repo is crucial for understanding the vulnerability’s severity – and how to fix it.
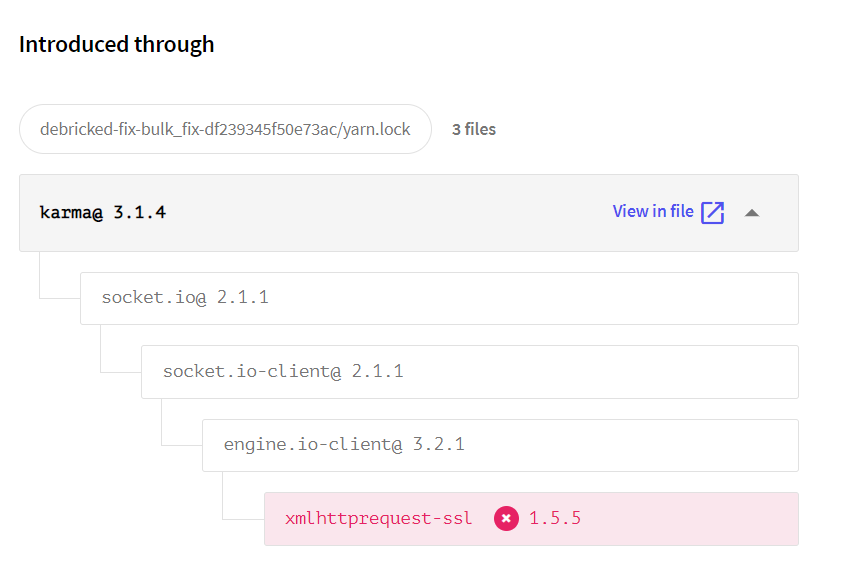
Say goodbye to hours of digging through your yarn.lock files and building your pom.xml files to figure out which indirect dependency belongs to which root dependency. Now you can use the visualization and instantly know.
Webhooks in Automations
Automations is a powerful tool to set up quality gates and enforce your organization’s open source policies in your CI/CD pipelines. But it’s been isolated from the larger context of your external workflows. Until now.
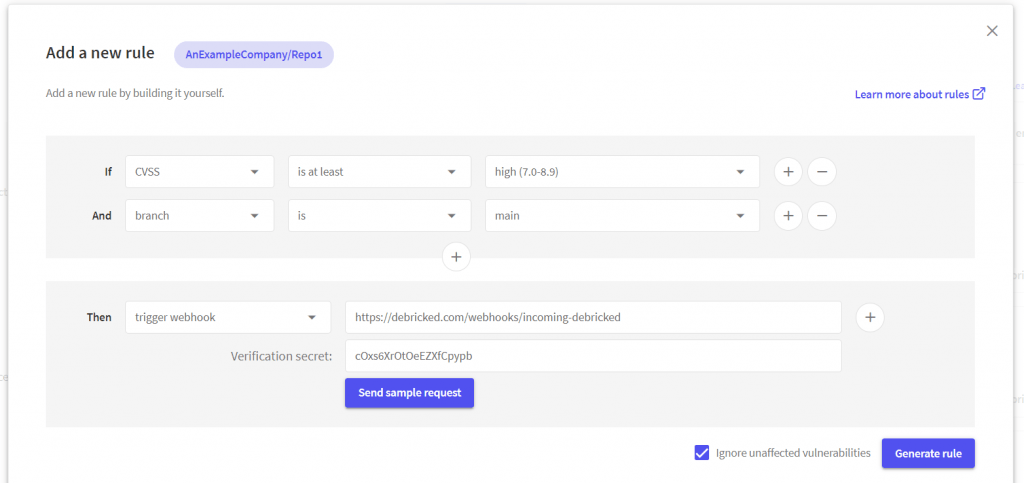
With the implementation of webhooks as an output option of an automation rule, open source management can truly become an integrated, and automated, part of your workflows.
The webhook returns a JSON with all conditions (dependencies, vulnerabilities, licenses) that triggered a certain rule, for you to use wherever it makes sense – be it in JIRA, Slack, a BI system or something completely different like setting of blinking lights and alarms when a vulnerability is found (probably shouldn’t do that, but you could).
You can write a few lines of code to transform the JSON into exactly what you want it to be, or use a system such as Zapier to handle that for you.
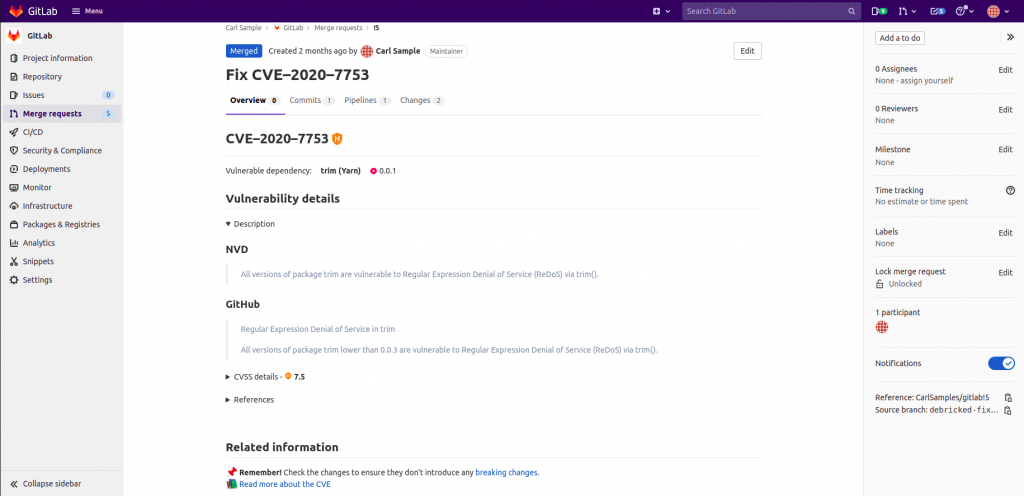
Fix Merge Request for GitLab
Fixing vulnerabilities is obviously essential to maintaining good open source security, but it can be hard. This spring we released Automatic Fix PRs for GitHub to help address this problem, now it’s also available for GitLab!
Open Source Select
If you haven’t yet read our release blogpost on open source select, you’re in for a treat.
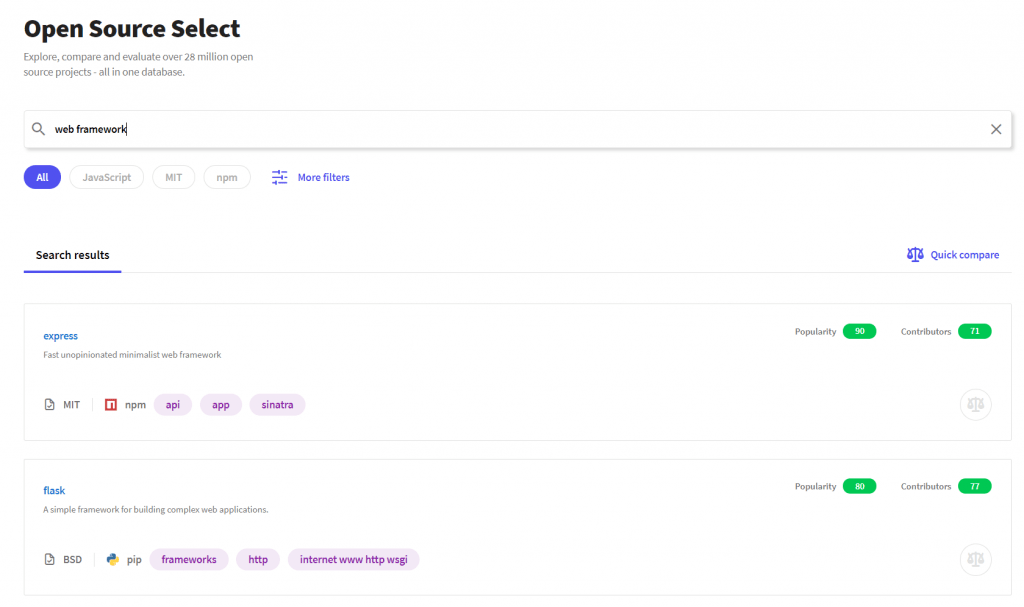
The TL;DR is that we’ve released an open, searchable database on open source projects, including the world’s first model for calculating metrics on how popular the projects are and how healthy their contributor communities are. You don’t need an account to use it, just visit debricked.com/select/ and start searching!
…and much more
Those were the main releases for this summer but that’s by no means an exhaustive list. Amongst other things we’ve also added:
Enforce comments when marking unaffected
To increase auditability, admins can now enable an option that forces users to leave a comment when a vulnerability is marked as unaffected.
Discovered Date in Automations
You can now set automations to trigger “x days” after a vulnerability was discovered. For example, this enables workflows where CI/CD pipelines throw warnings for the first 14 days after a vulnerability was discovered and subsequently fails them once 14 days have passed.
Filter out indirect dependencies
In the dependency tables (both global and per repo), indirect dependencies are now filtered out per default but can easily be toggled again. Filtering creates a less cluttered experience where you can differ between the dependencies that you’ve directly imported and their dependencies.


