
Introducing Root Fixes: Resolving transitive vulnerabilities with minimal effort

As a company, our most recent goal has been making it easy for users to fix their open source vulnerabilities. Our solutions have ranged from a simple fix suggestion to a super advanced pull request solving vulnerabilities through the click of a button. This new release is something in the middle. Behold, the Root Fix!
A new way of fixing open source vulnerabilities
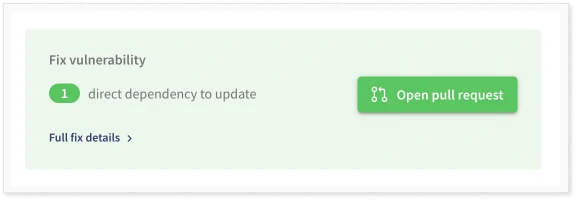
Fixing vulnerabilities is a tricky thing. We love our Fix Pull Request, where users can fix vulnerabilities with a button click, but we also understand the need for other alternatives. Both because some users want to fix things themselves and because our Fix Pull Request support is under development. To facilitate this, we’ve enabled something we call Root Fix, where we display the fix to our users, right there in our UI, allowing the choice between performing the fix manually or clicking our magic button.
So, how does it actually work?
Fixing open source vulnerabilities by updating the root
A Root Fix works the exact same way a Pull Request does – but instead of doing it for you we show you the entire dependency tree, the vulnerable version and the relationships, and how to fix it by yourself if you so prefer.
But wait… What do you mean by root?
The root refers to a direct dependency, which is a dependency that you’ve imported yourself. If a vulnerability exists in such a dependency the solution is quite simple: you just need to update that dependency to a safe version. Tadaa! Problem solved!
However, it’s not always that simple.
Indirect dependencies and indirect vulnerabilities
With direct dependencies come indirect dependencies, which are dependencies that you haven’t imported yourself but still can affect you. These little freeloaders make everything a bit more complicated and time-consuming. If there’s a vulnerability in an indirect dependency, depending on a direct dependency, you indirectly have a vulnerability and your code is no longer safe. How does one fix that?!
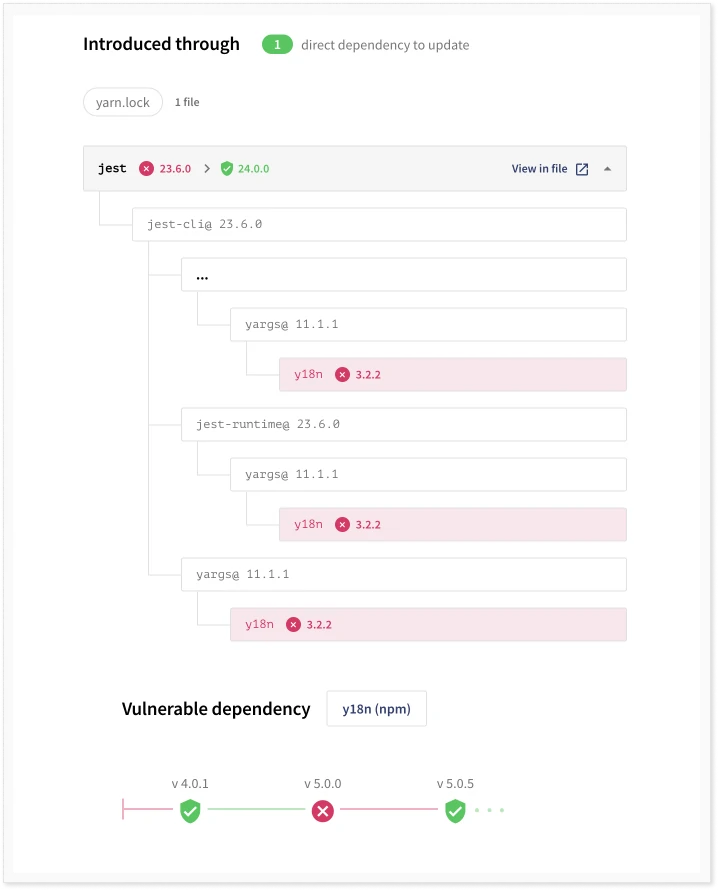
As seen in the picture, jest is the direct dependency, vulnerable due to it depending on y18n. In order to become secure, we need to update jest to a version which depends on a safe version of y18n.
Debricked to the rescue
Debricked helps you visualise your dependency tree, complete with direct and indirect dependencies, and show you the update needed to go from vulnerable to safe. We help you figure out which direct dependency needs to be updated in order to solve the indirect vulnerability. This saves you the headache of having to do this tedious investigation on your own – nice huh? You then have the choice to do it by yourself, manually, or click our magic button and fix it automatically.
Now, what are you waiting for? The Root Fix is now available for Javascript, with Java, C# and Go. Create a free account and try it out!
Please note that our support for Fix Pull Request at the moment extends to Javascript with GitHub app, GitLab and Azure DevOps. More support is to be rolled out in the coming months.


