
Debricked launches public vulnerability database
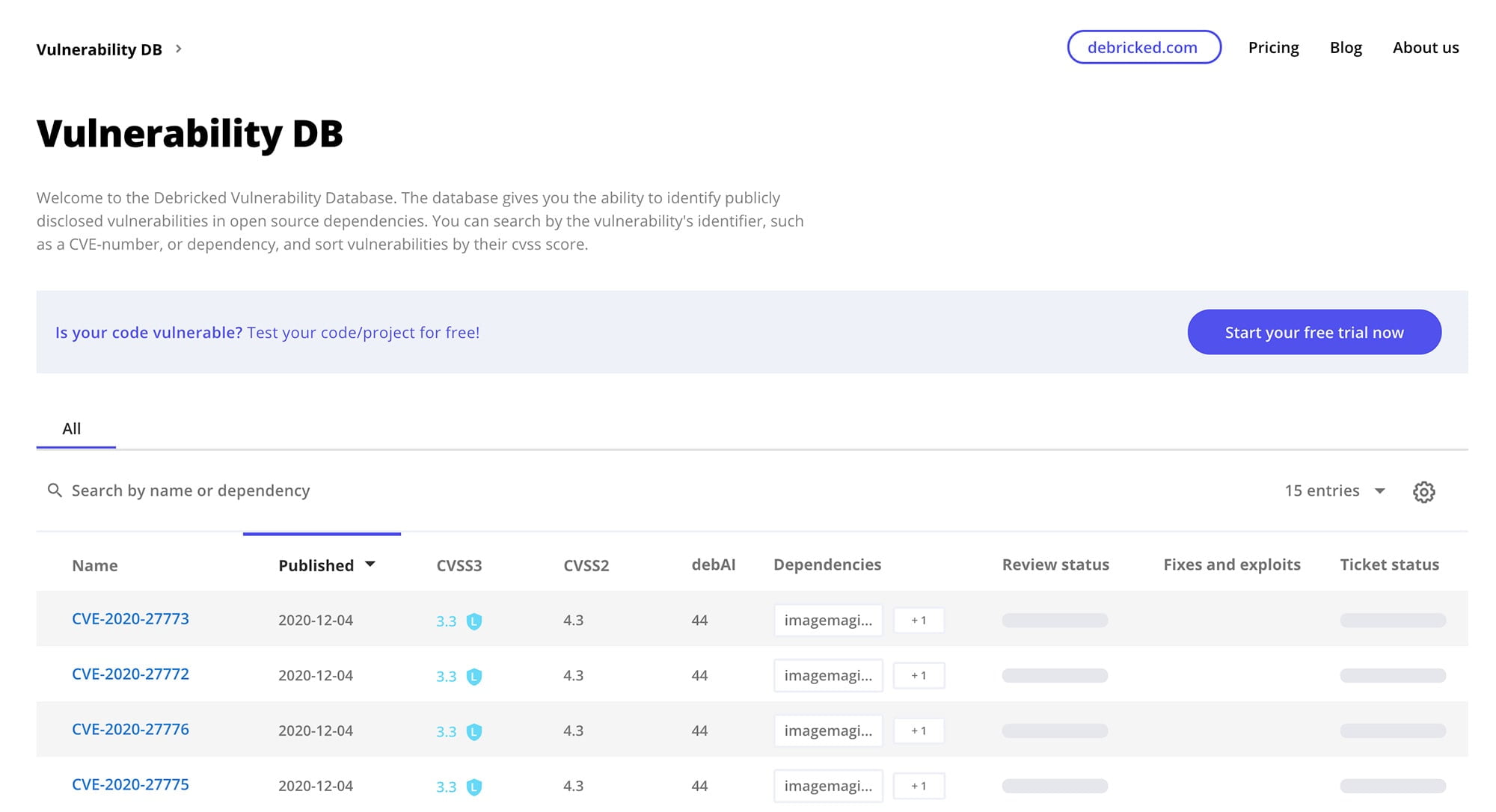
Today we are happy to announce that we have officially launched the Debricked vulnerability database, completely free of charge!
Built on the same technology empowering our security offering, in Debricked’s vulnerability database you will find vulnerabilities aggregated and curated from multiple sources.
These sources include NVD, GitHub Advisory Database (including NPM advisories), C# Announcements and more. This makes the Debricked Vulnerability Database one of the most comprehensive databases/advisories available.
Aggregated vulnerabilities
By aggregating data from multiple sources, we can provide you with the most detailed information for each vulnerability. For example, for a recently published vulnerability CVE-2020-15247, we are able to provide information from both GitHub and NVD:
Having multiple sources typically makes it easier to understand what the vulnerability is, whether you are affected or not and how to solve or workaround it. By providing both more extensive descriptions and more references, we bring you all the data you need to make an informed decision.
By aggregating the data, rather than showing the advisories as separate entries, we avoid duplicates and reduce noise. This way, we make it a lot easier and quicker to access the information you need.
Ease of use
While looking at vulnerabilities you might have come across a lot of new terminology such as CWE and CVSS. In our database, an explanation for these security related terms are always just one click away.
For example, when viewing a particular CVE, you probably want to have an understanding of its severity; the CVSS score. In the CVSS details you can read more about each individual metric which together constitutes a CVSS score, and whether the current value is good or bad. If you are really into security, we also have an extensive blog post on the matter.
Always up-to date and accurate
Compared to many other vulnerability databases we have no humans in the loop. Trusting algorithms instead makes it possible for us to provide a database which is constantly updated with no delay.
We also provide higher accuracy thanks to natural language processing, which can detect incorrectly labelled vulnerabilities, and preliminary labelling based on the description of vulnerabilities. This allows you to find vulnerabilities in your dependencies as soon as they are made public.
Start exploring the database today
Make sure to sign up for a free trial of our complete tool if you would like to automatically find which vulnerabilities affect your code base and get suggested fixes tailored to your repositories.

