You can integrate your Jenkins pipeline with Debricked, so that a vulnerability scan is performed every time the pipeline is triggered.
Configure Debricked token
Start by generating an access token. Copy the token to use it in the next step.
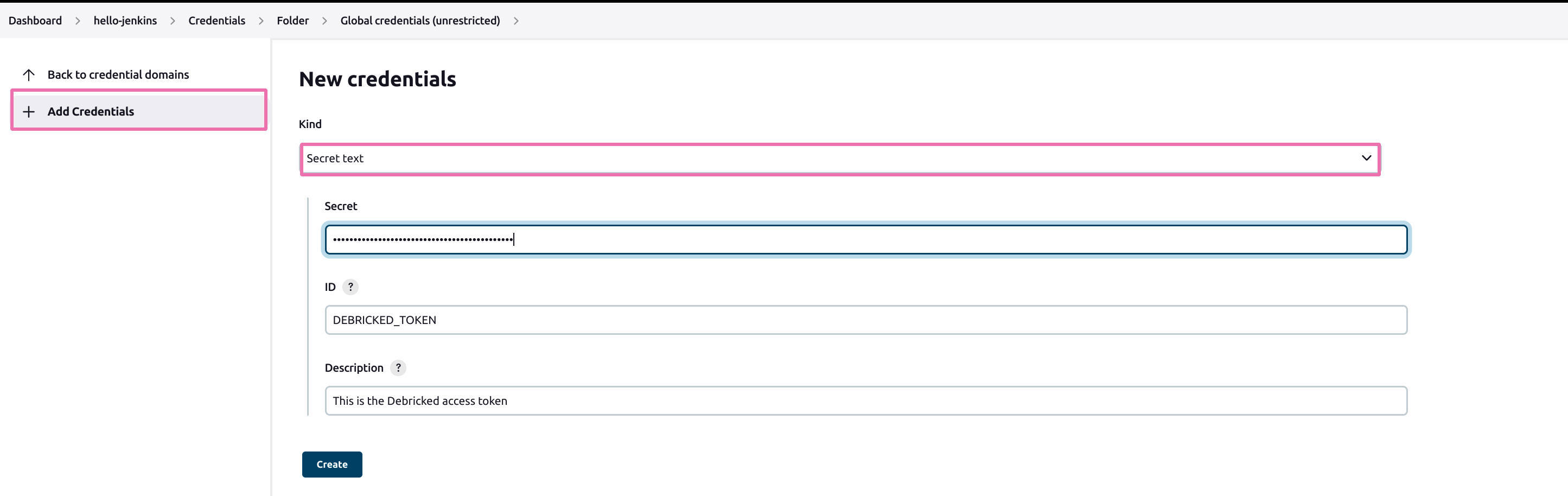
Create the DEBRICKED_TOKEN, which the pipeline will use. Inside Jenkins, go to your pipeline, click on “Add Credentials”, and select the correct folder. Create a new credential with "Kind" set to secret text. In the secret field insert the access token you created in the previous step. As ID, enter DEBRICKED_TOKEN and click on the button “Create”. See the image below:
Configure Jenkins CI Workflow
We assume you already have a Jenkinsfile in your repository, describing a declarative pipeline. You now need to add a new stage to this pipeline.
- Go to the following template and add it to the file
- Commit your changes to Jenkinsfile and watch the CI run!
